Cisco Certified Network Associate (CCNA) Routing and Switching is a certification program for entry-level network engineers that helps maximize your investment in foundational networking knowledge and increase the value of your employer's network. CCNA Routing and Switching is for Network Specialists, Network Administrators, and Network Support Engineers with 1-3 years of experience. The CCNA Routing and Switching validates the ability to install, configure, operate, and troubleshoot medium-size routed and switched networks
1 Refer to the exhibit.

The network administrator enters these commands into the R1 router:
R1# copy running-config tftp
Address or name of remote host [ ]?
When the router prompts for an address or remote host name, what IP address should the administrator enter at the prompt?
192.168.9.254192.168.10.1
192.168.10.2
192.168.11.254
192.168.11.252
2 Which three statements characterize the transport layer protocols? (Choose three.)
TCP uses port numbers to provide reliable transportation of IP packets.TCP and UDP port numbers are used by application layer protocols.
TCP uses windowing and sequencing to provide reliable transfer of data.
TCP is a connection-oriented protocol. UDP is a connectionless protocol.
UDP uses windowing and acknowledgments for reliable transfer of data.
3 What is the purpose of ICMP messages?
to inform routers about network topology changesto ensure the delivery of an IP packet
to monitor the process of a domain name to IP address resolution
to provide feedback of IP packet transmissions
4 A technician uses the ping 127.0.0.1 command. What is the technician testing?
connectivity between a PC and the default gatewayconnectivity between two adjacent Cisco devices
physical connectivity of a particular PC and the network
the TCP/IP stack on a network host
connectivity between two PCs on the same network
5 What will a Layer 2 switch do when the destination MAC address of a received frame is not in the MAC table?
It notifies the sending host that the frame cannot be delivered.It initiates an ARP request.
It forwards the frame out of all ports except for the port at which the frame was received.
It broadcasts the frame out of all ports on the switch.
6 What is a characteristic of the LLC sublayer?
It places information in the frame that allows multiple Layer 3 protocols to use the same network interface and media.It provides delimitation of data according to the physical signaling requirements of the medium.
It defines software processes that provide services to the physical layer.
It provides the logical addressing required that identifies the device.
7
On which switch interface would an administrator configure an IP address so that the switch can be managed remotely?
VLAN 1console 0
vty 0
FastEthernet0/1
8
A network engineer is measuring the transfer of bits across the company
backbone for a mission critical database application. The engineer
notices that the network throughput appears lower than the bandwidth
expected. Which three factors could influence the differences in
throughput? (Choose three.)
the reliability of the gigabit Ethernet infrastructure of the backbonethe amount of traffic that is currently crossing the network
the type of traffic that is crossing the network
the sophistication of the encapsulation method applied to the data
the bandwidth of the WAN connection to the Internet
the latency that is created by the number of network devices that the data is crossing
9
When applied to a router, which command would help mitigate brute-force password attacks against the router?
service password-encryptionlogin block-for 60 attempts 5 within 60
banner motd $Max failed logins = 5$
exec-timeout 30
10
Which two statements correctly describe a router memory type and its contents? (Choose two.)
ROM is nonvolatile and contains basic diagnostic software.FLASH is nonvolatile and contains a limited portion of the IOS.
ROM is nonvolatile and stores the running IOS.
RAM is volatile and stores the IP routing table.
NVRAM is nonvolatile and stores other system files.
11
Which two components are necessary for a wireless client to be installed on a WLAN? (Choose two.)
custom adapterwireless bridge
media
wireless NIC
crossover cable
wireless client software
12 Launch PT - Hide and Save PT

Open the PT activity. Perform the tasks in the activity instructions and then fill in the blank.
The Server0 message is . ” winner ”
13
A host is accessing a Web server on a remote network. Which three
functions are performed by intermediary network devices during this
conversation? (Choose three.)
applying security settings to control the flow of datanotifying other devices when errors occur
regenerating data signals
acting as a client or a server
serving as the source or destination of the messages
providing a channel over which messages travel
14
15

16
Which address on a PC does not change, even if the PC is moved to a different network?
IP addresslogical address
MAC address
default gateway address
17
What will happen if the default gateway address is incorrectly configured on a host?
A ping from the host to 127.0.0.1 would not be successful.The host will have to use ARP to determine the correct address of the default gateway.
The host cannot communicate with other hosts in the local network.
The host cannot communicate with hosts in other networks.
The switch will not forward packets initiated by the host.
18
A host PC has just booted and is attempting to lease an address through
DHCP. Which two messages will the client typically broadcast on the
network? (Choose two.)
DHCPREQUESTDHCPOFFER
DHCPDISCOVER
DHCPNACK
DHCPACK
19

Refer to the exhibit. An administrator wants to change the name of a brand new switch, using the hostname command as shown. What prompt will display after the command is issued?
Switch#My(config)#
My Switch(config)#
Switch(config)#
MySwitch(config)#
20
After making configuration changes, a network administrator issues a
copy running-config startup-config command in a Cisco switch. What is
the result of issuing this command?
The configuration changes will be removed and the original configuration will be restored.The new configuration will be stored in flash memory.
The current IOS file will be replaced with the newly configured file.
The new configuration will be loaded if the switch is restarted.
21

Refer to the exhibit.A TCP segment from a server has been captured by Wireshark, which is running on a host. What acknowledgement number will the host return for the TCP segment that has been received?
2921250
2
306
21
22
Which technology provides a solution to IPv4 address depletion by allowing multiple devices to share one public IP address?
ARPDNS
SMB
DHCP
HTTP
NAT
23 What is the purpose of the routing process?
to encapsulate data that is used to communicate across a networkto select the paths that are used to direct traffic to destination networks
to convert a URL name into an IP address
to provide secure Internet file transfer
to forward traffic on the basis of MAC addresses
24 Three bank employees are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other corporate managers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types?
audio conference, financial transactions, web pagefinancial transactions, audio conference, web page
audio conference, web page, financial transactions
financial transactions, web page, audio conference
25
A home user is looking for an ISP connection that provides high speed
digital transmission over regular phone lines. What ISP connection type
should be used?
cell modemdial-up
cable modem
satellite
DSL
26
Which connection provides a secure CLI session with encryption to a Cisco switch?
a Telnet connectionan SSH connection
a console connection
an AUX connection
27 What is the purpose of the network security accounting function?
to provide challenge and response questionsto require users to prove who they are
to determine which resources a user can access
to keep track of the actions of a user
28

Refer to the exhibit. A network administrator is configuring access
control to switch SW1. If the administrator uses Telnet to connect to
the switch, which password is needed to access user EXEC mode?
lineconinlinevtyin
letmein
secretin
29
Which publicly available resources describe protocols, processes, and
technologies for the Internet but do not give implementation details?
IEEE standardsRequest for Comments
IRTF research papers
protocol models
30 A PC is configured to obtain an IP address automatically from network 192.168.1.0/24. The network administrator issues the arp –a command and notices an entry of 192.168.1.255 ff-ff-ff-ff-ff-ff. Which statement describes this entry?
This entry refers to the PC itself.This entry maps to the default gateway.
This is a static map entry.
This is a dynamic map entry.
31 Which subnet would include the address 192.168.1.96 as a usable host address?
192.168.1.64/26192.168.1.32/28
192.168.1.32/27
192.168.1.64/29
32
A particular website does not appear to be responding on a Windows 7
computer. What command could the technician use to show any cached DNS
entries for this web page?
ipconfig /allipconfig /displaydns
arp -a
nslookup
33 Which type of wireless security generates dynamic encryption keys each time a client associates with an AP?
WPAPSK
WEP
EAP
34
A frame is transmitted from one networking device to another. Why does the receiving device check the FCS field in the frame?
to compare the interface media type between the sending and receiving endsto determine the physical address of the sending device
to verify that the frame destination matches the MAC address of the receiving device
to check the frame for possible transmission errors
to verify the network layer protocol information
35

Refer to the exhibit. Which IP addressing scheme should be changed?
Site 1Site 3
Site 4
Site 2
36
What is the effect of configuring the ipv6 unicast-routing command on a router?
to assign the router to the all-nodes multicast groupto permit only unicast packets on the router
to enable the router as an IPv6 router
to prevent the router from joining the all-routers multicast group
37
Which three IP addresses are private ? (Choose three.)
10.1.1.1172.16.4.4
224.6.6.6
192.168.5.5
172.32.5.2
192.167.10.10
38

Refer to the exhibit. Consider the IP address configuration shown from PC1. What is a description of the default gateway address?
It is the IP address of the Router1 interface that connects the company to the Internet.It is the IP address of the ISP network device located in the cloud.
It is the IP address of Switch1 that connects PC1 to other devices on the same LAN.
It is the IP address of the Router1 interface that connects the PC1 LAN to Router1.
39 During normal operation, from which location do most Cisco switches and routers run the IOS?
flashRAM
NVRAM
disk drive
40
What is an important function of the physical layer of the OSI model?
It encodes frames into electrical, optical, or radio wave signals.It accepts frames from the physical media.
It encapsulates upper layer data into frames.
It defines the media access method performed by the hardware interface.
41
Which procedure is used to reduce the effect of crosstalk in copper cables?
wrapping the bundle of wires with metallic shieldingavoiding sharp bends during installation
requiring proper grounding connections
designing a cable infrastructure to avoid crosstalk interference
twisting opposing circuit wire pairs together
42
What are the three primary functions provided by Layer 2 data encapsulation? (Choose three.)
placement and removal of frames from the mediadetection of errors through CRC calculations
conversion of bits into data signals
delimiting groups of bits into frames
data link layer addressing
error correction through a collision detection method
session control using port numbers
43
What method is used to manage contention-based access on a wireless network?
token passingCSMA/CD
CSMA/CA
priority ordering
44
What happens when part of an Internet radio transmission is not delivered to the destination?
A delivery failure message is sent to the source host.The part of the radio transmission that was lost is re-sent.
The transmission continues without the missing portion.
The entire transmission is re-sent.
45
What is the auto-MDIX feature on a switch?
the automatic configuration of full-duplex operation over a single Ethernet copper or optical cablethe automatic configuration of an interface for a straight-through or a crossover Ethernet cable connection
the ability to turn a switch interface on or off accordingly if an active connection is detected
the automatic configuration of an interface for 10/100/1000 Mb/s operation
46
Which function is provided by TCP?
detection of missing packetscommunication session control
path determination for data packets
data encapsulation
47
How does a Layer 3 switch differ from a Layer 2 switch?
A Layer 3 switch learns the MAC addresses that are associated with each of its ports. However, a Layer 2 switch does not.A Layer 3 switch maintains an IP address table instead of a MAC address table.
A Layer 3 switch supports VLANs, but a Layer 2 switch does not.
An IP address can be assigned to a physical port of a Layer 3 switch. However, this is not supported in Layer 2 switches.
48
Which two notations are useable nibble boundaries when subnetting in IPv6? (Choose two.)
/68/62
/66
/64
/70
49
What is the purpose of having a converged network?
to reduce the cost of deploying and maintaining the communication infrastructureto provide high speed connectivity to all end devices
to make sure that all types of data packets will be treated equally
to achieve fault tolerance and high availability of data network infrastructure devices
50

Refer to the exhibit. A ping to PC3 is issued from PC0, PC1, and PC2 in
this exact order. Which MAC addresses will be contained in the S1 MAC
address table that is associated with the Fa0/1 port?
just the PC0 MAC addressPC0, PC1, and PC2 MAC addresses
just the PC2 MAC address
just PC0 and PC1 MAC addresses
just the PC1 MAC address
51
Which field in an IPv4 packet header will typically stay the same during its transmission?
Packet LengthDestination Address
Flag
Time-to-Live
52
What two preconfigured settings that affect security are found on most new wireless routers? (Choose two.)
MAC filtering enableddefault administrator password
WEP encryption enabled
PSK authentication required
broadcast SSID
53
Which parameter does the router use to choose the path to the destination when there are multiple routes available?
the higher metric value that is associated with the destination networkthe lower metric value that is associated with the destination network
the higher gateway IP address to get to the destination network
the lower gateway IP address to get to the destination network
54

Refer to the exhibit. What is the significance of the asterisk (*) in the exhibited output?
An asterisk designates that the file system has at least one file that uses that file system.The asterisk designates which file system is the default file system.
An asterisk indicates that the file system is bootable.
The asterisk shows which file system was used to boot the system.
55

56
Fill in the blank.
During data communications, a host may need to send a single message to a specific group of destination hosts simultaneously. This message is in the form of a ” multicast ” message.57
An administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes?
to interrupt the ping processto restart the ping process
to allow the user to complete the command
to exit to a different configuration mode
58

Refer to the exhibit. Which area would most likely be an extranet for the company network that is shown?
area Aarea D
area C
area B
59

60

61
In which default order will a router search for startup configuration information?
setup mode, NVRAM, TFTPNVRAM, TFTP, setup mode
NVRAM, RAM, TFTP
TFTP, ROM, NVRAM
flash, ROM, setup mode
62

Launch PT - Hide and Save PT
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
Which IPv6 address is assigned to the Serial0/0/0 interface on RT2?
2001:db8:abc:1::12001:db8:abc:5::1
2001:db8:abc:5::2
2001:db8:abc:10::15
63
What is contained in the trailer of a data-link frame?
physical address
data
error detection*
logical address
4.
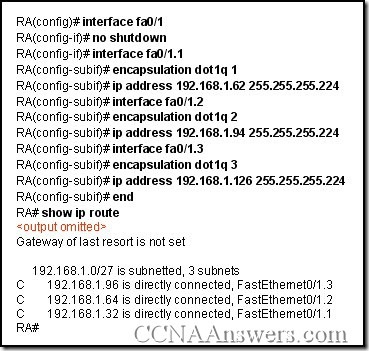
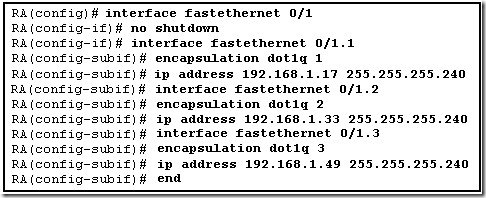
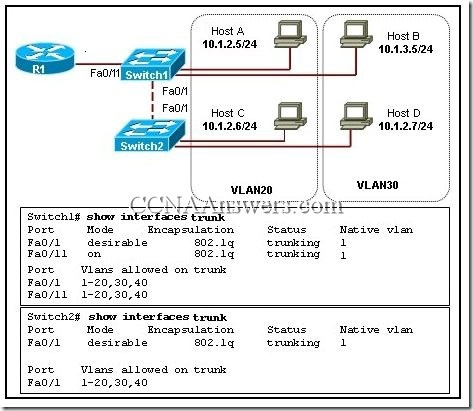
Refer to the exhibit. Router RA receives a packet with a source address of 192.168.1.65 and a destination address of 192.168.1.161. What will the router do with this packet?
The router will drop the packet.
The router will forward the packet out interface FastEthernet 0/1.1.
The router will forward the packet out interface FastEthernet 0/1.2.
The router will forward the packet out interface FastEthernet 0/1.3.
The router will forward the packet out interface FastEthernet 0/1.2 and interface FastEthernet 0/1.3.
5.
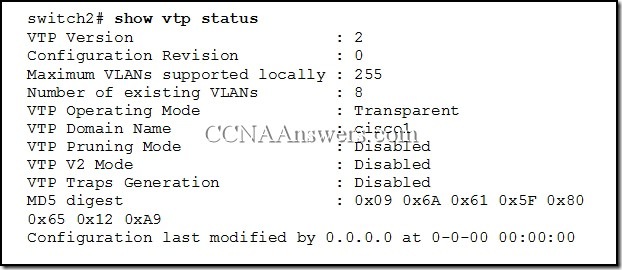
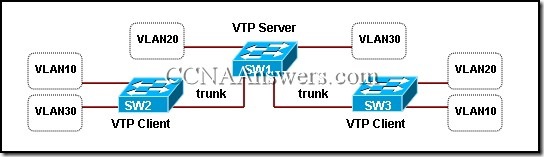
Refer to the exhibit. Which two settings show the default value of VTP configuration on a Cisco 2960 switch? (Choose two.)
revision number
existing VLANs
operating mode
domain name
pruning mode
6. Which value determines if a switch becomes the central point of reference in the spanning tree topology?
lowest bridge ID
highest revision number
lowest numeric IP address
highest numeric MAC address
7. What is the purpose of the Spanning Tree algorithm?
It propagates VLAN configurations to other switches.
It restricts broadcast packets to a single VLAN.
It segments a network into multiple broadcast domains.
It prevents loops in a switched network with redundant paths.
8. What are two benefits of the IEEE 802.11n standard over the IEEE 802.11G? (Choose two.)
requires less equipment
provides improved range
permits increased data rates
has a single-input and a single-output
needs no hardware upgrade for compatibility
9. Which configuration changes will increment the configuration revision number on the VTP server?
configuring trunk links on the VTP server
configuring or changing the VTP password
configuring or changing the VTP domain name
configuring or changing the VTP version number
configuring or deleting a VLAN or creating a VLAN name
10.
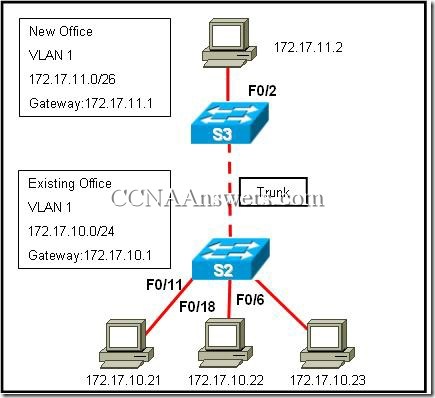
Refer to the exhibit. A company has acquired a new office in a campus environment. Switches in the existing office and the new office are directly connected by a trunk link. The VLANs and IP addressing are setup as shown in the exhibit. The computers in each office are not able to ping each other. What will fix the problem?
Use an access link between S2 and S3.
Connect S2 and S3 to a common router.
Set the subnet mask in the new office to /24.
Configure the new office default gateway to 172.17.10.1
Change the port assignments in the new office to a different VLAN.
11. What is a possible impact of setting too short an aging time in the MAC address table of a switch?
overly large address table
unnecessary flooding of packets
excessive timeouts of static addresses
impaired ability to dynamically learn new addresses
12.
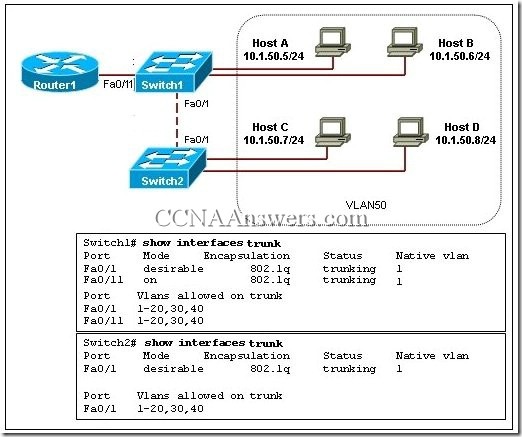
Refer to the exhibit. The network administrator has just added VLAN 50 to Switch1 and Switch2. Hosts A, B, C, and D are correctly configured with IP addresses in the subnet range for VLAN 50. Host A can communicate with host B, but cannot communicate with host C or host D. What is the cause of this problem?
There is a native VLAN mismatch.
The Fa0/11 interface of Switch1 is not configured as a trunk.
The link between Switch1 and Switch2 is up but not trunked.
VLAN 50 is not allowed on the trunk link between Switch1 and Switch2.
13.
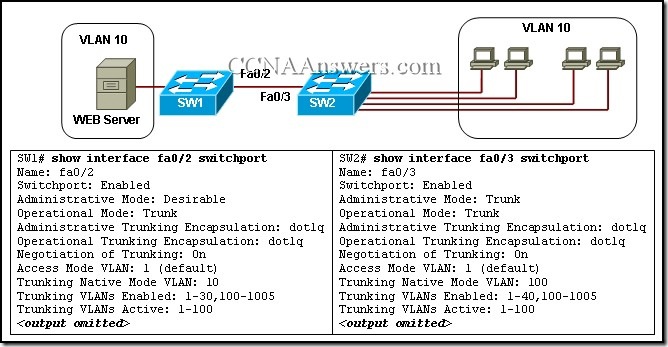
Refer to the exhibit. Users complain that they do not have connectivity to the web server that is connected to SW1. What should be done to remedy the problem?
Allow all VLANs on the trunk link.
Configure VLAN 100 as the native VLAN for SW1.
Configure the trunk port in trunk mode on SW1.
Attach the web server to a router and configure inter-VLAN routing.
14. What VLANs are allowed across a trunk when the range of allowed VLANs is set to the default value?
only the management VLAN
all VLANs except the extended range VLANs
all VLANs except 1 and 1002-1005
all VLANs
15.
Refer to the exhibit. A new host needs to be connected to VLAN 1. Which IP address should be assigned to this new host?
192.168.1.11 /28
192.168.1.22 /28
192.168.1.33 /28
192.168.1.44 /28
192.168.1.55 /28
16. Using the command copy tftp:backup.cfg startup-config, an administrator downloaded a saved configuration from a TFTP server to a switch. Why does the administrator not detect any changes in the switch configuration after the download completes?
The command should have been copy startup-config tftp:backup.cfg.
A backup configuration from a TFTP server cannot be copied directly into the startup-config.
The command copy running-config startup-config should be used to save the changes on the switch.
Downloading to the startup-config requires the switch to be reloaded in order for the configuration to take effect.
17. What two methods can be used to remove MAC address table entries from a switch? (Choose two.)
Power cycle the switch to clear all dynamically learned addresses.
The clear switching-tables command will remove statically configured entries.
The clear mac-address-table command will remove statically and dynamically configured table entries.
The erase flash command will clear all statically configured table entries.
Statically configured MAC addresses will automatically be removed from the address table 300 minutes after the last activity on a switch port.
18. Which type of traffic can still be received on a switch interface that is in STP blocking mode?
BPDU frames
multicast frames
broadcast frames
Layer 3 packets
19. Which method establishes an administrative connection for configuring the Linksys WRT300N wireless access point?
Associate with the access point and then open a HyperTerminal session with the access point.
Physically connect to the access point and then reboot the computer to launch the configuration software.
From a computer in the same IP subnet as the access point, enter the default IP address of the access point in a web browser.
Modify the TCP/IP properties of the computer connected to the access point so that it exists on the same network, and then reboot your computer to establish a connection.
20.

Refer to the exhibit. All edge ports are configured with the spanning-tree portfast command. Host1 is recently connected to port Fa0/1 on switch SW1 . Which statement is true about the status of port Fa0/1?
The port will transition into blocking state.
The port will transition immediately into forwarding state.
The port will transition into blocking state and then immediately into forwarding state.
The port will transition into blocking state and immediately transition through the listening and learning states.
21.
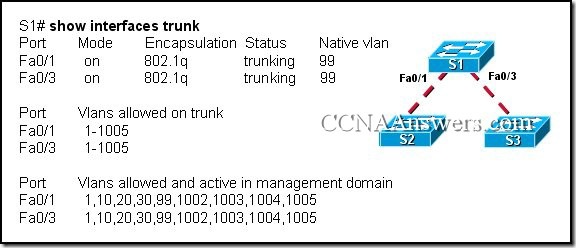
Refer to the exhibit. What is true of the configuration of switch S1?
A Cisco proprietary protocol is in use for ports Fa0/1 and Fa0/3.
Switch ports Fa0/1 and Fa0/3 have been configured with the switchport mode access command.
Untagged frames received on ports Fa0/1 and Fa0/3 will be placed on VLAN 1.
Switch ports Fa0/1 and Fa0/3 are configured to carry data from multiple VLANs.
22.
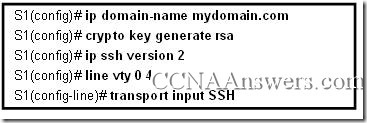
Refer to the exhibit. The configuration steps that are listed in the exhibit have been entered in switch S1 via the console. Subsequent attempts to telnet to the switch are not successful. What is causing the problem?
The switch must be configured with SSH version 1.
The transport input command must specify Telnet access.
The RSA keys must be returned to zero before SSH will permit Telnet access.
The ip domain-name command must also be entered in line configuration mode for the vty lines.
23.
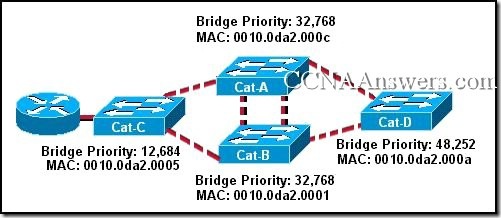
Refer to the exhibit. Which switch will be elected as the root bridge of the spanning tree topology?
Cat-A
Cat-B
Cat-C
Cat-D
24.

Refer to the exhibit. VTP has been configured with VTP pruning enabled on all switches. If HostA sends a broadcast frame to SW1, which devices will receive the frame?
SW1, SW3, HostF
SW1, HostB, HostC
SW1, SW2, SW3, SW4, HostF
SW1, SW2, SW3, SW4, all hosts
25.
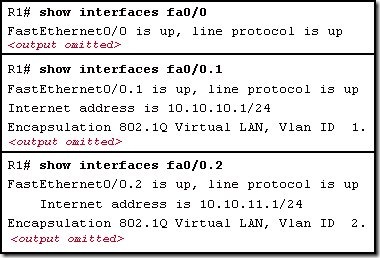
Refer to the exhibit. Which two statements are true about the operation of the interfaces? (Choose two.)
Incoming traffic with VLAN ID 0 is processed by interface fa0/0.
Incoming traffic that has a VLAN ID of 2 is processed by subinterface fa0/0.2.
Both subinterfaces remain up with line protocol up, even if fa0/0 line protocol is down.
Subinterfaces use unique MAC addresses by adding the 802.1Q VLAN ID to the hardware address.
Traffic inbound on this router is processed by different subinterfaces, depending on the VLAN from which the traffic originated.
26. The network administrator wants to configure a switch to pass VLAN update information to other switches in the domain but not update its own local VLAN database. Which two steps should the administrator perform to achieve this? (Choose two.)
Reset the VTP counters.
Configure VTP version 1 on the switch.
Configure the VTP mode of the switch to transparent.
Verify that the switch has a higher configuration revision number.
Configure the switch with the same VTP domain name as other switches in the network.
27.
Refer to the exhibit. The devices in the network are operational and configured as indicated in the exhibit. However, hosts B and D cannot ping each other. What is the most likely cause of this problem?
The link between the switches is up but not trunked.
The Fa0/11 interface of Switch1 is not configured as a trunk.
Hosts B and D are configured with IP addresses from different subnets.
VLAN 20 and VLAN 30 are not allowed on the trunk between the switches.
28.
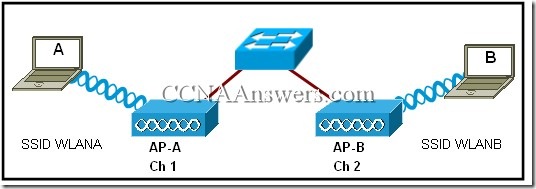
Refer to the exhibit. Users A and B are reporting intermittent connectivity problems. Pre-installation surveys showed strong signal strength from the AP locations to the client locations. Outside electrical interference has been eliminated. What will fix the problem?
Relocate the APs closer to each other.
Increase the distance between the clients.
Change the channel on AP-B to 6 or 11.
Place AP-A and AP-B on the same wireless channel.
29. Why is it advisable that a network administrator use SSH instead of Telnet when managing switches?
SSH uses TCP whereas Telnet does not.
SSH encrypts only the username and password when logging in.
SSH encrypts all remote management communications whereas Telnet does not.
SSH sends a clear text message steam which reduces the bandwidth use for management.
30.

Refer to the exhibit. The teacher host is connected to port Fa0/7 on switch STW. A student has decided to share access to the Internet by attaching a hub and laptop to STW as shown. What will be the result of the student making this connection?
The Fa0/7 port of STW will be shutdown.
The student will gain full access to the Internet.
Both the teacher and student will be able to receive data but only the teacher will be able to send.
The frames from the laptop will be dropped, but the teacher host will maintain connectivity with the network.
31. A network administrator configures a switch port with the command switchport mode dynamic auto. What is the resulting behavior of the switch port?
The switch port is able to trunk if the remote switch port is set to auto.
The switch port is able to trunk if the remote switch port is set to desirable.
The switch port will be disabled if it is unable to successfully negotiate trunking.
A successful trunk will be established if the remote switch is non-Cisco but the port is configured for trunking.
32. Which STP port type can only appear once on a segment, and must be present in order for traffic to flow on that segment?
non-root port
disabled port
designated port
non-designated port
33.
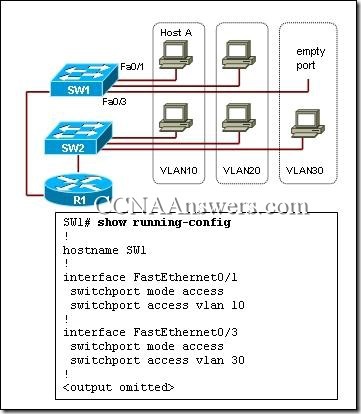
Refer to the exhibit. What would happen if the network administrator moved the network cable of Host A from interface Fa0/1 to Fa0/3 on switch SW1?
Host A remains a member of VLAN 10, because the router is routing traffic between VLANs.
Host A is no longer a member of VLAN 10, because port Fa0/3 has been manually assigned to VLAN 30.
Host A remains a member of VLAN 10, because the switch provides dynamic VLAN assignment for the port.
Host A maintains connectivity to all members of VLAN 10, because it is connected to the same physical network.
Host A is no longer a member of VLAN 10, but because port Fa0/3 was unused, it is now a member of VLAN 1.
34.
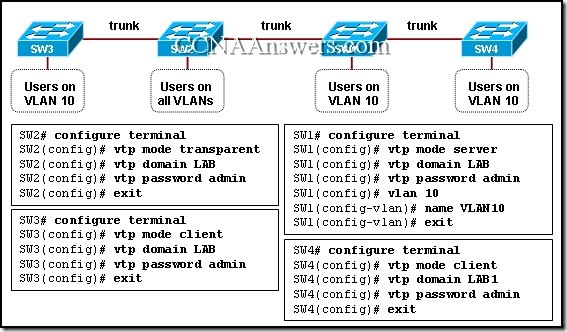
Refer to the exhibit. VLAN 10 has been configured on the VTP server. Users who are assigned to VLAN 10 are connected as shown in the exhibit. On the basis of the outputs that are provided, which group of users will be able to communicate with the users on VLAN 10 on SW1?
all the users who are connected only to SW2
users on VLAN 10 who are connected only to SW3
users on VLAN 10 who are connected only to SW4
users on VLAN 10 who are connected to both SW3 and SW4
35.
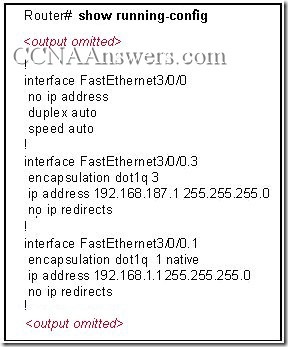
Refer to the exhibit. Which three options correctly identify information that could be associated with this output?(Choose three.)
Interface FastEthernet3/0/0 is subinterfaced.
A non-proprietary trunking protocol is in use.
The configuration is appropriate for a router-on-a-stick network design.
A shutdown command has been applied to interface FastEthernet3/0/0.
Interface FastEthernet3/0/0.3 is mapped to the default management VLAN.
An IP address should be applied to FastEthernet3/0/0 for correct data routing.
36.
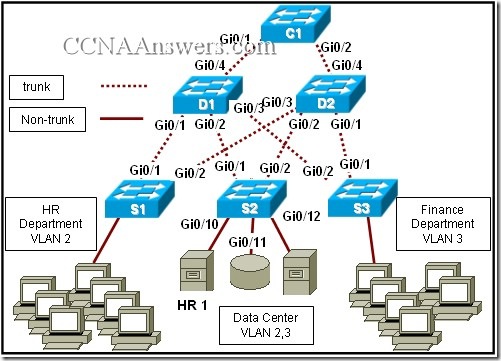
Refer to the exhibit. The Layer 2 switching design that is shown has been implemented in a campus environment that is using Spanning Tree Protocol. All inter-switch links that are shown are trunks. Whenever an inter-switch link fails, the network takes nearly a minute to completely converge. How can the convergence time be reduced?
Increase the capacity of the distribution and core trunk links to 10 Gb/s.
Add a trunk link that directly connects D1 and D2.
Use Layer 3 switching on the core switch.
Implement Rapid Spanning Tree Protocol.
37.
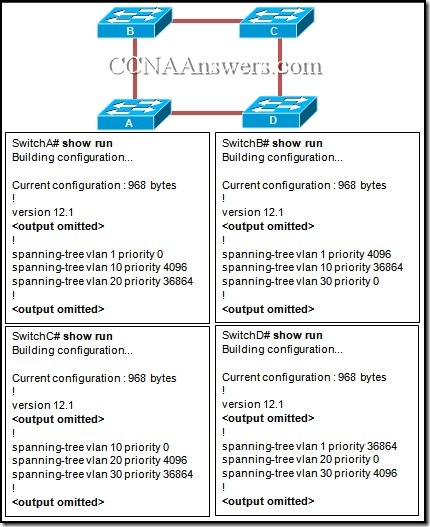
Refer to the exhibit. Each switch is configured to participate in STP for VLANs 1, 10, 20, and 30. Which switch will become the root for VLAN 20?
A
B
C
D
38.
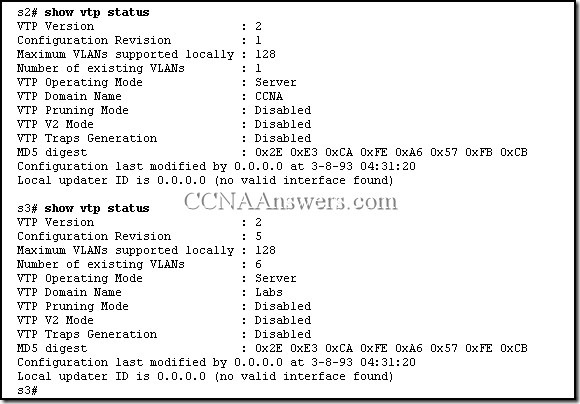
Refer to the exhibit. Switches S2 and S3 are properly connected using an ethernet cable. A network administrator has configured both switches with VTP, but S3 is unable to propagate VLANs to S2. What could be the reason for this?
The VTP configuration revision is different on both switches.
The VTP domains are different on both switches.
VTP pruning is disabled.
VTP v2 is disabled.
39. In a three-layer hierarchical network design, which distribution layer function delineates broadcast domains?
routing between VLANs
aggregating traffic flows
providing redundant links
reducing the network diameter
40. Which parameter is used to uniquely identify one wireless network from another?
SSID
OFDM
WEP
DSSS
41. What is one disadvantage that 802.11a wireless has compared to 802.11g?
Use of the 5GHz band requires much larger antennas.
The OFDM modulation technique results in a slower data rate.
There are fewer non-overlapping channels available to help reduce RF interference.
The use of higher frequencies means that signals are more likely to be obstructed.
42. Which three statements are correct concerning the default configuration of a new switch? (Choose three.)
It is configured in VTP server mode.
STP is automatically enabled.
The first VTY line is automatically configured to allow remote connections.
VLAN1 is configured with a management IP address.
All switch ports are assigned to VLAN1.
The enable password is configured as cisco.
43.
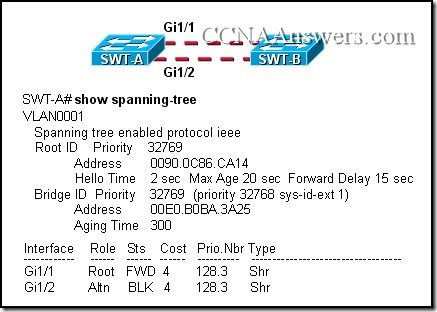
Refer to the exhibit. How is port Gi1/1 on SWT-A functioning in the spanning-tree topology?
It is sending and receiving data frames.
It is receiving BPDUs, but not sending data frames.
It is participating in the election process by forwarding the BPDUs it receives.
It is receiving BPDUs and populating the MAC address table, but not sending data.
44. While configuring a new switch, a network administrator configures the switch as an HTTP server. What benefits does this configuration provide?
This allows the switch to host web pages for the network.
This allows remote VPN connections to the switch over the Internet.
This is required if a web server or web farm is attached to the switch.
This allows web-based configuration tools to be used with the switch.
45. Which statement describes the use of voice VLANs in Cisco IP telephony?
The voice VLAN carries both tagged and untagged traffic.
The voice VLAN carries untagged traffic having special QoS markings.
The voice VLAN must be configured on the switch port to which the IP phone attaches.
Data and voice frames are tagged with same VLAN ID between the IP phone and the switch when a voice VLAN is configured.
46.
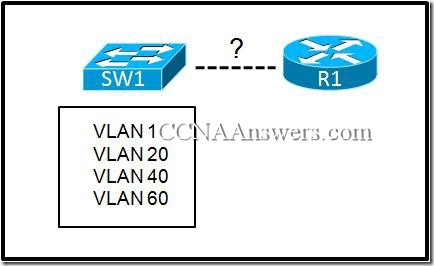
Refer to the exhibit. If switch SW1 is configured with the four VLANs as shown in the exhibit, how many physical interfaces are needed on router R1 to configure inter-VLAN routing using subinterfaces?
zero
one
two
four
47.
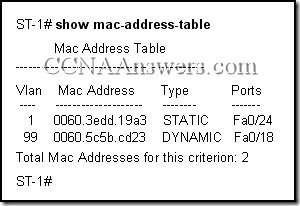
Refer to the exhibit. What does the term DYNAMIC indicate in the output that is shown?
This entry can only be removed from the MAC address table by a network administrator.
When forwarding a frame to the device with address 0060.5c5b.cd23, the switch does not have to perform a lookup to determine the final destination port.
Only the device with MAC address 0060.5c5b.cd23 will be allowed to connect to port Fa0/18.
The switch learned this MAC address from the source address in a frame received on Fa0/18.
48.
Refer to the exhibit. The VTP domain has been configured as shown in the exhibit. The network technician accidentally configured the VTP server as a VTP client. After the technician reloaded the switches, all users in the VTP domain started to complain that they lost connectivity to the users on the same VLANs that are connected to other switches. What should be done in the future to prevent losing all VLAN configurations in a VTP domain?
Configure all switches in VTP transparent mode and copy the VLAN configuration into flash.
Configure all switches in the network as VTP clients and copy the VLAN configuration into NVRAM.
Create a new domain and configure a second switch as a VTP server to take over in case of a primary VTP server failure.
In the same domain, configure a second switch as a VTP server to take over in case of a primary VTP server failure.
49.

Refer to the exhibit. How does SW1 manage traffic coming from Host A?
SW1 drops the traffic because it is untagged.
SW1 leaves the traffic untagged and forwards it over the trunk.
SW1 tags the traffic with the lowest VLAN ID value and forwards it over the trunk link.
SW1 encapsulates the traffic with 802.1Q encapsulation and forwards it over the trunk link.
50. An administrator is troubleshooting a PC on the network which is suffering from slow and intermittent connectivity. The PC has a ping success rate to the default gateway of less than half the ping attempts. Other PCs on the switch can consistently ping the default gateway. The switch port is configured for auto duplex and the PC is configured for full duplex. What will commonly cause this problem?
The PC is set to full duplex. The switch port fails to autonegotiate the duplex setting and defaults to half duplex, which causes a duplex mismatch.
The switch traffic is exceeding available frame buffers. The result is that frames are being dropped.
The PC and the default gateway have different bandwidth Ethernet ports.
The default gateway is not on the same switch that the PC is.
51.
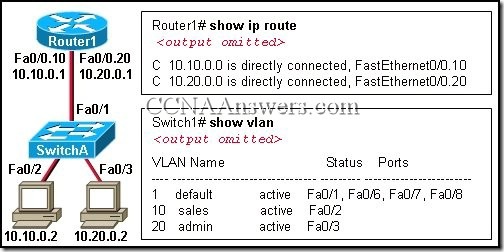
Refer to the exhibit. A network administrator has segmented the network into two VLANs and configured Router1 for inter-VLAN routing. A test of the network, however, shows that hosts on each VLAN can only access local resources and not resources on the other VLAN. What is the most likely cause of this problem?
Switch port Fa0/1 is not trunking.
Router interface Fa0/0 is possibly down.
No routing protocol is configured on Router1.
One of the router subinterfaces is possibly down.
52. What impact does the use of the mdix auto configuration command have on an Ethernet interface on a switch?
automatically detects duplex settings
automatically detects interface speed
automatically detects copper cable type
automatically assigns the first detected MAC address to an interface
64


No comments:
Post a Comment
Your Comment Please
This Blog is Do Follow